Contents
What is ICE-159?
ICE-159 is a type of bot malware that allows a hacker to take control of the affected computer. Once ICE-159 has taken control of your system, it can perform a variety of automated tasks that can display strange messages, slow down your system, or even crash it. With ICE-159, a hacker can steal your confidential information by sending spam, refusing certain services on the Internet and even committing "click fraud".
ICE-159 is usually created not to compromise a single computer, but to infect millions of devices. Bot shepherds often use ICE-159 on computers via a Trojan horse virus. The strategy usually requires users to infect their own systems by opening email attachments, clicking on malicious pop-ups or downloading dangerous software from a website. Once the devices are infected ICE-159 is then free to access and modify personal information, attack other computers and commit other crimes.
More complex ICE-159 can even spread, find and automatically infect devices. These autonomous robots perform search and infection missions and constantly search the Internet for vulnerable devices connected to the Internet, without updating the operating system or antivirus software.
ICE-159 is difficult to detect. It consumes little computing power so as not to interfere with the normal functions of the device and warn the user. More advanced ICE-159 are even designed to update their behavior to prevent their detection by cybersecurity software. Users are not aware that the connected device is controlled by cybercriminals. Worse still, the ICE-159 design is constantly evolving, making new versions more difficult to find.
ICE-159 takes time to grow. Many of them will sleep in devices waiting for the botmaster to ask them to take action in case of a DDoS attack or to spread spam.
ICE-159 Details
- Bot Name: ICE-159
- Risk Level: Medium
- File Length: 159 bytes
- Subtype: File Infector
- Category: Bots
ICE-159 Aliases
ICE-159 is also known by these other aliases:
- SillyIce.159
- Silly_Ice.159
- Virus.DOS.ARCV.Ice.159
- Univ/a
- ICE-159
- Silly Ice.159
What are Bots?

Bots, (short for robots,) are also known as spiders, crawlers and web robots. Although they can be used for recurring tasks such as indexing a search engine, they are often in the form of malware. Malware is used to take full control of a computer.
One of the "good" applications typical of a bot is the collection of information. Bots dressed like this are called "b crawlers". Another "good" application is automatic interaction with instant messaging, instant relay chat or various other web interfaces. Dynamic interaction with websites is another way to use robots for positive purposes.
Malicious robots are defined as self-produced malware that infects their host and reconnects to one or more central servers. The server serves as a "command and control center" for a botnet or network of vulnerable computers and similar devices. Malicious robots have the "ability to spread like worms" and can also:
- Collect passwords
- Memorize keystrokes on the keyboard
- Obtaining financial information
- Forward spam
- Capture and analysis of packaging
- Launch DoS attacks
- Open the back doors of the infected computer.
- Use backdoors opened by viruses and worms.
Bots are generally used to infect a large number of computers. These computers form a "botnet" or bot network.
How did ICE-159 get on my PC?
Like other malware, bots are often accidentally downloaded to a computer by email, phishing messages that ask the recipient to click on a link or social media messages that try to get you to download an image or click on a link.
Advanced malware generally reaches a computer or network through the following distribution channels:
- Unwanted download of computer software from the Internet
- Unsolicited emails - Unsolicited attachments or links embedded in the email
- Physical media - Integrated or removable media such as USB sticks
- Self-propagation - the ability of malware to move from one computer to another or from one network to another and thus to spread itself.
Symptoms of ICE-159?
The main symptoms of ICE-159 infections are:
- The computer is behaving strangely
- Slow start, stop and performance
- Excessive CPU usage
- Shortcuts to files and folders are displayed.
- Change the default settings of your browser's search engine and home page
- Unsolicited emails that constantly appear in your inbox.
- Spam emails sent from your inbox without your knowledge.
- New programs and files are automatically added.
- Unexpected pop-ups appear in your browsers.
- The antivirus and firewall settings are automatically changed.
How to remove ICE-159 from your PC?
If you suspect an infection, take the following steps to find out what is happening:
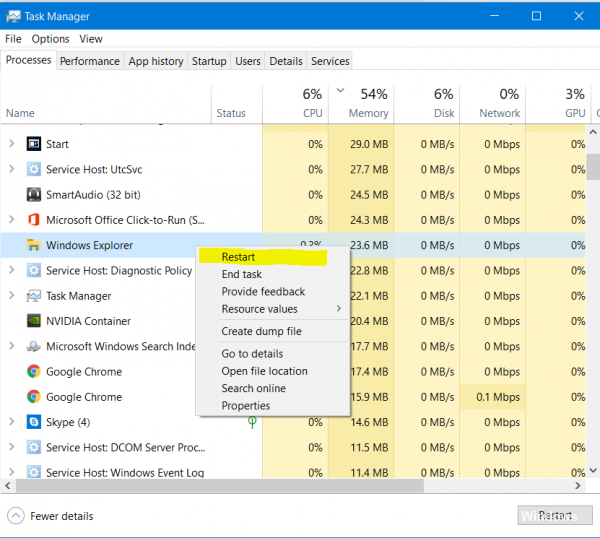
Use Windows Task Manager, or rather the Sysinternal Process Explorer, to search for applications that don't seem to belong or that seem to consume a large amount of system resources. Chances are you won't find a bot directly this way, but the information your system gives you can help you move in the right direction.
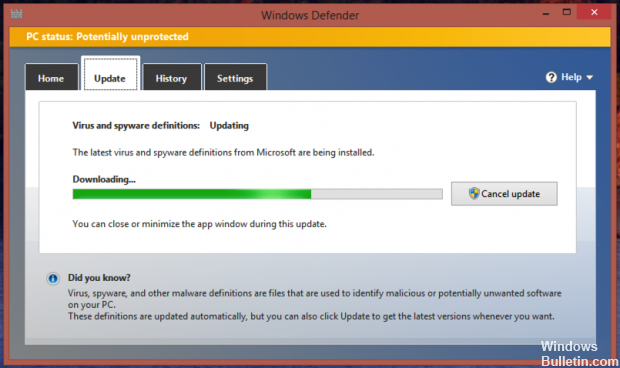
Your next step (as obvious as it may seem) is to make sure that you have checked your system with the latest antivirus signatures. I also strongly recommend using Anti-Rootkit tools. Again, this is not a guaranteed solution, but you must do it anyway. If you find a bot or related malware at this stage, you may be able to remove the code with the appropriate tool. However, as with rootkits, the only crucial way to remove a bot from your system is to save, reformat and reload it.
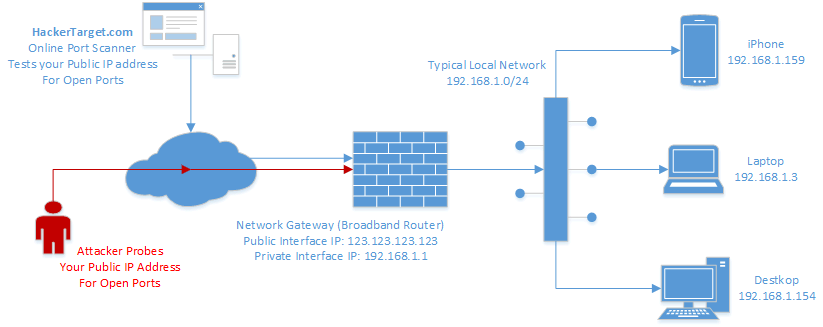
Then scan your systems for open ports and vulnerabilities. You can kill two birds with one stone by using a vulnerability scanner that shows you which ports are open and which vulnerabilities exist. In addition, you can use a vulnerability scanner as a proactive and preventive measure during your ongoing security scans. Be sure to scan all your systems - servers, workstations, etc. - for viruses. Any Windows host is a fair game for a bot infection.
How To Fix & Remove ICE-159
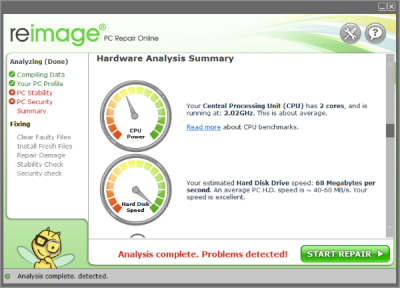
You can download this tool from the official download page. The installation is quite routine and simple. Once installed, you will need to run it. The tool automatically analyzes your computer and displays errors, viruses, malware and relevant issues that need to be fixed. The full analysis takes a little longer, but provides complete coverage and security. The results of the analysis are very detailed and you can determine which part of your computer is slowing down.
Here are the areas or things that are diagnosed during the process:
- System and hardware configuration
- PC stability
- Computer Security
- register analysis
- Scanning temporary folders
After reviewing the results of the analysis, it is time to start troubleshooting. All you have to do is click on the Start Repair button and your work is done. Reimage corrects problems that occur with prescribers and also performs another in-depth analysis to solve other problems.
Summary
The only way to avoid malicious robots is not to click on links from sources you do not fully trust. This includes downloads by email or links provided by email or social media websites.
Make sure your system is always up to date and that your antivirus program is working to provide you, your family and friends with additional protection.