Are you looking for a PC update and restore solution that is reliable and easy to use? If so, then you may want to consider Restoro. This software has been gaining in popularity over the past few years, and for good reason. It is one of the most comprehensive backup and restore solutions on the market today. In this article, we will take a closer look at what Restoro has to offer, and see if it is the right solution for you.
| Feature | Description |
|---|---|
| Windows Errors (including BSoD) | Restoro can easily recognize and fix any Windows errors, including the Blue Screen of Death. It does so by identifying the source of the error and replacing or fixing the relevant files using its 25.000.000 file database. |
| Damaged DLLs | Restoro can identify and fix damaged or missing DLL files using its updated DLL file database. |
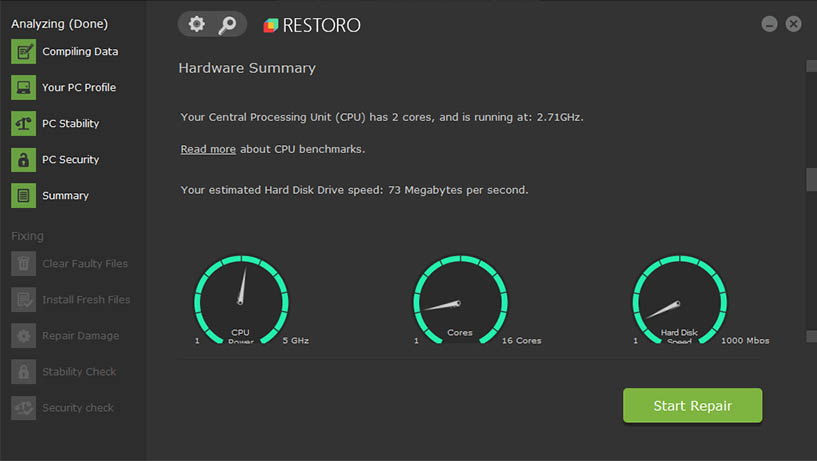
| System crashes | Restoro can detect files and applications that are crashing frequently and allow you to fix their problems with a single click. It also provides information on hardware details and the PC’s operating temperature. |
| Removes spyware and malware | Restoro can detect and remove malware, as well as repair any damage caused by it. It replaces corrupted or missing files that were altered or removed by the malware. |
| PC stability improvements | Restoro removes viruses and repairs any damage done, including replacing corrupted system files. It is designed to handle the side effects that other antivirus software may not be able to fix, such as crashes and missing files. |
| Diagnoses issues automatically | Restoro can automatically identify issues even before they impact the system and suggest the best way to resolve them. Options may include removing, replacing, or repairing the file. |
| Cleans duplicated or corrupted files | Based on the diagnosis and suggested fixes, Restoro can automatically clean or replace duplicated or corrupted system files. |
| Optimizes system for best speeds | Restoro can optimize your system to improve its speed and performance. It does this by identifying and fixing any issues that may be causing slowdowns. |
| Restores system performance | Restoro can restore your system’s performance by fixing any issues that may be causing it to run poorly. |
| Easy to use | Restoro is user-friendly and easy to use, requiring only a single click to start the fixing process. |
| Wide range of supported systems | Restoro supports a wide range of systems, including Windows 10, 8, 7, Vista, and XP. |
| Large file database | Restoro’s database of 25.000.000 files allows it to accurately replace or fix any necessary files. |
| Automatic updates | Restoro’s developers are constantly working to update the software and its file database to ensure the best performance. |
How safe is Restoro?
The internet is full of software programs that claim to be able to repair your computer. Many of these programs are scams, but some, like Restoro, are legitimate. So, is Restoro safe?
Yes, Restoro is a safe and effective way to repair your computer. The program works by scanning your computer for errors and then fixing them automatically. Additionally, Restoro will back up your data before making any changes, so you can always revert back if something goes wrong.
Restoro is easy to use and has a very user-friendly interface. Simply download the program and run the scan. Once the scan is complete, you’ll see a list of all the errors that were found on your computer. Just click “Fix” to repair them.
What can Restoro fix?
Restoro is a PC repair and optimization tool that can help to fix a wide variety of problems on your computer. It can repair registry errors, corrupt files, and even malware damage. In addition, Restoro can also help to improve your computer’s performance by optimizing your system settings and cleaning up junk files. Whether you’re dealing with a slow computer or unwanted pop-ups, Restoro can help to get your PC back on track. While it’s not a replacement for a full antivirus program, Restoro can be a valuable tool for keeping your computer healthy.
Windows Errors (BSOD etc)
Restoro can fix a variety of computer problems, including the dreaded blue screen of death (BSoD). Restoro is designed to work with Windows 10, 8, 7, Vista, and XP. The program can fix registry errors, file permissions issues, and corrupted system files. Restoro can also restore your computer to a previous state if it has been infected by malware or if you have made changes to the system that you want to undo. In addition, the program can automatically backup your system before making any changes, so you can always revert back if something goes wrong. Overall, Restoro is a versatile and user-friendly PC repair tool that is worth checking out if you are having problems with your computer.
Damaged or Missing DLLs
Restoro can be used to fix a variety of issues, including damaged or missing DLL files. DLL files are dynamic link library files that are used by Windows to run programs. When a DLL file is damaged or missing, it can cause errors and crashes. Restoro can scan your system for damaged DLL files and replace them with working copies. This can fix many common problems, such as blue screen errors and program crashes. In addition, Restoro can also be used to clean up your registry and optimize your system for better performance. Overall, Restoro is a powerful tool that can be used to fix a variety of PC problems.
Windows System crashes
If you’ve ever experienced a system crash, you know how frustrating it can be. Your computer suddenly shuts down, and you lose all your work. Even worse, you may not be able to restart your computer at all.
Restoro can fix a wide range of issues, including system crashes. It works by scanning your computer for errors and then repairing them automatically. In most cases, you’ll be able to restart your computer and continue working without any further problems.
Can remove malware & spyware
While no single program can catch everything, Restoro is a reliable and effective tool that can help get rid of many types of spyware and malware. And best of all, it’s easy to use. Just download and install the program, then run a scan. Restoro will scan your computer for malicious files and then remove them. It also comes with a free trial, so you can try it out before you buy it.
Improvement of PC stability
PC optimization software is designed to help improve your computer’s performance by fixing common issues and improving stability. Restoro offers a wide range of features to help you get the most out of your PC. One of the most useful features is the ability to repair damaged or corrupt files. This can be extremely helpful if you’ve been experiencing errors or crashes, as it can help to fix the underlying cause. In addition, Restoro can also help to improve startup times and overall stability by cleaning up your system registry and managing running processes.
Automatic issue diagnoses
Restoro diagnoses and fixes common issues automatically. It uses a powerful combination of registry cleaning, file recovery, and malware removal to fix your PC, and it’s all done in just a few clicks. Restoro is one of the most comprehensive PC repair tools on the market, and it’s also one of the easiest to use. Just download and install Restoro, then run a scan. Restoro will automatically detect and fix any problems it finds. And if you’re not happy with the results, you can always revert back to a previous restore point.
Corrupted/duplicated file cleaning
Have you ever downloaded a file only to find that it’s corrupt or that there are multiple copies of it on your hard drive? If so, then you know how frustrating it can be to deal with duplicated or corrupted files. Fortunately, Restoro can help you clean up these issues. Restoro works by scanning your hard drive for duplicate or corrupt files and then repairing or deleting them as needed. The program is very easy to use and doesn’t require any technical expertise. Simply launch the program, select the files you want to clean up, and let Restoro do its job. In just a few minutes, you’ll have a clean hard drive with no duplicated or corrupted files.
Speed Optimization
System optimization is always a top priority for any computer user. This is because a slow and sluggish system can be very frustrating to use. Restoro comes with a lot of features that make it very effective in optimizing your system. One of the best features of Restoro is its ability to clean up your registry. The registry is a database that stores all the settings and options for your computer. Over time, the registry can become cluttered with redundant and obsolete entries. This can cause your system to slow down and become unstable. Restoro’s registry cleaner will scan you registry and remove all the unwanted entries, leaving you with a clean and optimized registry. This will help to improve your system’s speed and stability.
Restoro cannot repair 3rd party apps
While Restoro is a great app for repairing corrupted or damaged files on your computer, it is important to note that it does not repair or replace third-party apps. However, Restoro can be used to fix other issues such as registry errors, blue screen of death errors, and file corruption. Overall, Restoro is a great tool for repairing damaged files on your computer, but it is important to keep in mind that it does not repair or replace third-party apps.
System requirements
Restoro is available as a free download for Windows 7 and up. Before you can use Restoro, you’ll need to meet the following system requirements:
- 2 GB of RAM
- 200 MB of free hard drive space
- An internet connection for downloading and activating the program
- A compatible web browser (Chrome, Firefox, or Edge)
Once you’ve downloaded and installed Restoro, simply launch the program and click “Scan Now.” Restoro will scan your system for common problems and attempt to fix them automatically.

How does it work?
One of the key features of Restoro is its ability to fix registry errors. The registry is a database that stores information about your computer’s hardware and software. Over time, the registry can become cluttered with outdated or incorrect entries, which can lead to problems such as crashes and freezes. Restoro can scan your registry and identify any potential errors. Once it has located the problems, it can then fix them quickly and easily, restoring your computer to its optimal performance. In addition to registry repairs, Restoro can also perform other optimizations, such as removing junk files and defragmenting your hard drive. As a result, Restoro can help to improve your computer’s speed and stability.
Is Restoro free?
It’s free to download, but there is a fee if you want to unlock all the features.
How much does Restoro cost?
The cost of Restoro varies depending on the license type you choose. A single-user license costs $29.95, while a five-user license costs $39.95. A business license is also available for $49.95. Restoro is a great option if you’re looking for an all-in-one solution to fix your PC. It’s especially helpful if you’re not comfortable with manually editing your system settings or installing third-party software.
Other useful features
In addition to its file repair and Windows restoration capabilities, Restoro also offers a number of other useful features. For instance, it can create a full system backup, allowing you to quickly restore your PC if something goes wrong. It can also help you uninstall unwanted programs and remove malware from your system. Overall, Restoro is an extremely versatile tool that can be used to fix a wide range of PC problems.
How to fix Windows errors using Restoro
Windows errors can be frustrating. They can popup at the most inopportune times and prevent you from using your computer. But luckily, there are a few simple steps you can take to fix most Windows errors.
The Restoro software will scan your computer for any missing or corrupt files and then replace them with fresh copies. This often fixes common errors like DLL errors and registry errors.
The second step is to run a full system scan with Restoro. This will check for any other issues that may be causing problems on your system. If any are found, they will be automatically fixed.
The third and final step is to restart your computer. After Restoro has made the necessary changes to your system, it’s important to restart your computer to ensure that the changes take effect. Once you’ve restarted, you should find that your Windows errors have been fixed.
What is the difference between Restoro and other PC repair software?
Restoro is a PC repair software that has been designed to help users fix a wide range of PC problems. Restoro uses a cloud-based system to scan and repair your PC. The software also includes a range of features, such as the ability to restore lost files and create backups. In addition, Restoro can be used to repair a wide range of PC problems, including registry errors, file corruptions, and malware infections. However, how does Restoro compare with other PC repair software?
In terms of features, Restoro is very similar to other PC repair software. However, where Restoro really stands out is in its ease of use. The software has been designed to be user-friendly, and the interface is extremely intuitive. Even if you’ve never used a PC repair tool before, you should be able to use Restoro with ease.
Another area where Restoro shines is in its price. The software is available for both Windows and Mac, and a single-user license costs just $29.95. A five-user license costs $39.95, and a business license costs $49.95. This makes Restoro one of the most affordable PC repair tools on the market.
When it comes to customer support, Restoro is also excellent. The software comes with a 30-day money-back guarantee, so you can try it risk-free. In addition, the Restoro website includes a comprehensive knowledge base, and the customer support team is always on hand to answer any questions you may have.
Overall, Restoro is a great PC repair tool that offers a wide range of features and is extremely easy to use. It’s also very affordable, and the customer support is excellent. If you’re looking for a PC repair tool, be sure to give Restoro a try.
Who is Restoro intended for?
Restoro is a PC repair and maintenance tool that can be used by anyone who wants to keep their computer in top shape. The software is designed to fix common problems, such as registry errors and file corruption, that can lead to slow performance and stability issues. Restoro can also be used to perform basic cleanup tasks, such as removing junk files and unwanted programs. However, the software is not a replacement for a professional technician, and it should only be used as a last resort when other methods of fixing computer problems have failed. Restoro is available for both Windows and Mac computers, and a free trial is available for those who want to try the software before purchasing a license.
Our conclusion on Restoro
If you’re looking for a reliable and effective system repair tool, Restoro is definitely worth considering. It’s easy to use, even for beginners, and it can quickly fix a wide range of common PC problems. Best of all, it comes with a 60-day money back guarantee, so you can try it risk-free.
Of course, no tool is perfect, and Restoro is no exception. One potential downside is that it doesn’t work with every type of problem. Additionally, some users have reported that the software can be slow to scan and repair your system.
Overall, though, Restoro is a great option for anyone who wants an easy way to fix common PC issues. With its 60-day money back guarantee, there’s no reason not to give it a try.
Have you used Restoro? What was your experience? Let us know in the comments below.

