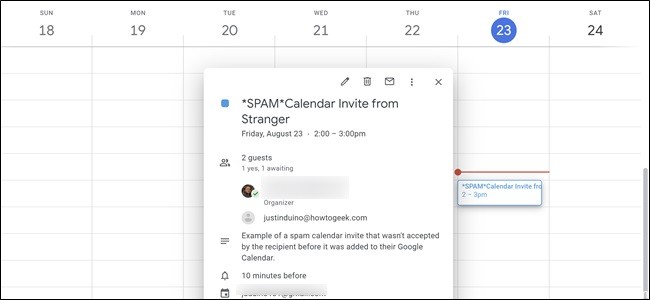
Spammers have found a way to add unwanted phishing and scam events to users’ Google calendars without their consent. This will prevent spammers from adding things to your agenda without your permission.
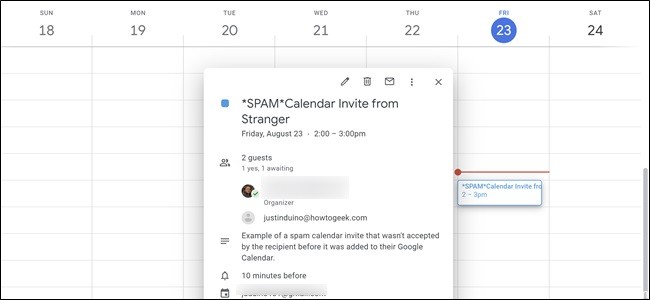
At this point, you are probably looking for possible phishing messages in your email. You know the procedure: If you have any doubts, do not click on the links or download the attachments. This is already difficult enough to follow in practice. Thanks to the Kaspersky threat research company’s new findings, as well as phishing texts, phishing tweets and phishing pop-ups, you now have another thing to worry about: Phishing in your calendar.
Phishers have realized that they can use the seemingly harmless settings of the calendar to place their own events with phishing links on the victims’ agenda. In many cases, it also automatically triggers notifications, which further legitimizes malicious events. Scams are particularly effective because calendar entries and notifications come from trusted applications such as Google Calendar.
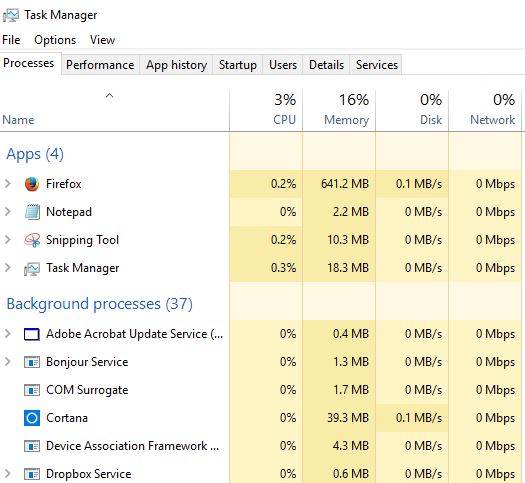
The attack simply comes from crooks who send a wave of calendar events to Google Calendar users. The goal is to use the default setting that target calendars automatically add each event and send a notification about it. Scammers therefore preload the text from the event entry with a phishing link and a short line to make the targets click.
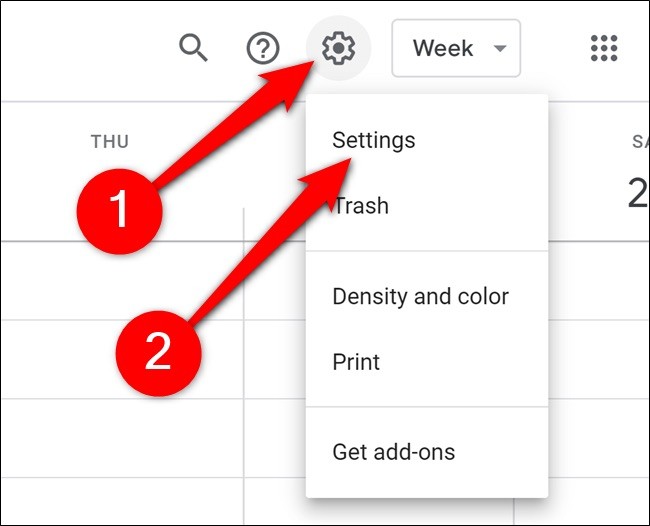
To prevent the Calendar from automatically adding invitations
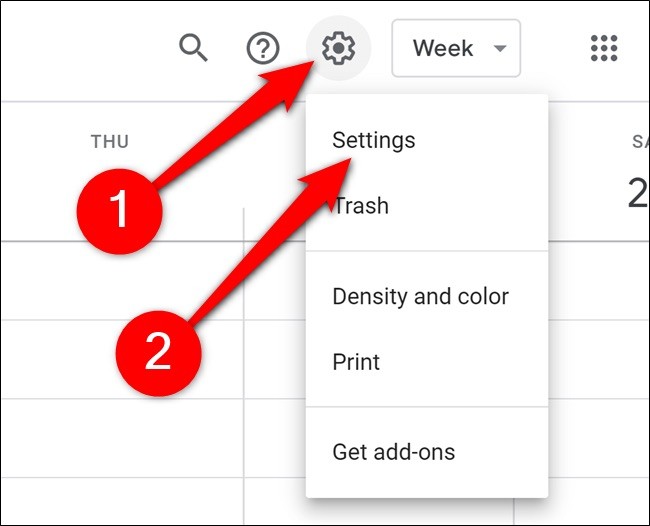
This prevents your calendar from automatically adding calendar invites:
- Go to the Settings menu by clicking on the icon at the top right of the calendar page, then selecting “Settings” from the drop-down menu.
- Select Event Settings from the left sidebar.
- Click on the “Automatically add invitations” page.
- From the drop-down menu, select “No, only display invitations to which I have replied”.
You can also prevent it from adding events from Gmail by going to the Preferences menu and clicking Go:
- Select “Gmail Events” from the left sidebar.
- Uncheck the box “Automatically add Gmail events to my calendar”.
Again, it’s a kind of all or nothing, so if you like this feature, you might not want to change your settings before calendar spam becomes a problem.
However, if calendar spam already gives you a headache, this can be a quick and easy way to solve it.
Stop Calendar From Adding Events From Gmail

Google Calendar also pulls events directly from Gmail. When someone sends you an invitation – sometimes even when it goes into the spam folder – it arrives in your calendar. To disable this function, return to the Settings menu by clicking on the report icon and selecting Settings.
- Then select “Gmail Events” from the left sidebar.
- Uncheck the box “Automatically add Gmail events to my calendar”.
- Google Calendar will ask you to confirm this action. Click OK to confirm the change.
Hide Declined Events

If you have had spam invitations in the past, but are tired of seeing the crossed-out entries, you can get rid of them by using the following method:
- Go to “View Options” in the left menu.
- Make sure that the “Show rejected events” option is not checked.
Unfortunately, this does not affect the way you view rejected events on your phone. To ensure that rejected events do not appear on your phone:
Select the three parallel lines at the top left of the calendar to display the side menu.
Scroll down and select “Settings”.
Select “General”.
Look for “Show declined events” and make sure it is disabled.
read more