Updated April 2024: Stop getting error messages and slow down your system with our optimization tool. Get it now at this link
- Download and install the repair tool here.
- Let it scan your computer.
- The tool will then repair your computer.
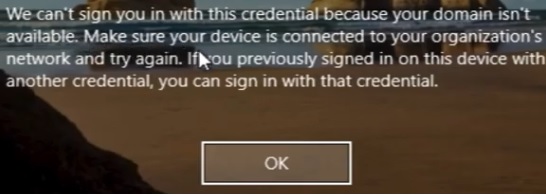
If you’re having trouble signing into your Microsoft account after installing a new monthly update or running an antivirus scan, you may receive the “we can’t sign you in with this credential” or “You’ve been signed in using a temporary profile” error message when you attempt to log in. If this occurs, then the system has signed you in using a new temporary account, instead of the one you originally used, and any changes you made in this session will be lost once you sign out.
Fortunately, if you end up having a temporary account on Windows, there are several sets of steps that will help you to recover from this situation. Here, we’ll walk you step by step through a number of ways to troubleshoot and resolve these errors.
What does it mean when it says your domain isn’t available
When a PC or laptop belongs to an organization, in order to log into it, it must verify that the computer and the account belong to the organization. It ensures that the system doesn’t use its resources until they’re authorized. However, if the PC cannot connect to a domain via the local intenet or the internet, then it will show this error.
How to get rid of the ‘we can’t sign you in with this credential’ error message
Restart the system with no network connectivity

To read the status of the systems link to the organization, you need to be connected to the internet. However, a lesser-known fact is that we don’t actually need to log into the system to connect it to the internet. If any network was set to “default”, the system would connect to it before reaching the lock screen. In order to isolate this issue, we’d need to disconnect the network from there.
- Click on the “Network Connectivity” icon on the bottom-left corner of the screen.
- Open the “Internet Connection Settings”.
- Select “Mobile Broadband”
- Uncheck the box next to “Connect Automatically.”
- Save the changes.
- Restart the system.
- Re-enter the password and log in to the system.
April 2024 Update:
You can now prevent PC problems by using this tool, such as protecting you against file loss and malware. Additionally it is a great way to optimize your computer for maximum performance. The program fixes common errors that might occur on Windows systems with ease - no need for hours of troubleshooting when you have the perfect solution at your fingertips:
- Step 1 : Download PC Repair & Optimizer Tool (Windows 10, 8, 7, XP, Vista – Microsoft Gold Certified).
- Step 2 : Click “Start Scan” to find Windows registry issues that could be causing PC problems.
- Step 3 : Click “Repair All” to fix all issues.
Remove the user from the protected user group
When you add a user to a protected user group, he gets access to some features that are unavailable to others. This is useful when you want to limit what a specific person can do on a certain system. However, there is a downside to adding people to such groups. When someone tries to log into the system, they usually receive an error stating that they cannot log in because they are not part of the protected user group.
The solution is simple: just remove the user from the group. You might think that this will break things, but it won’t. In fact, it will probably work better than trying to fix the problem later.
Using Security Policy snap-in
- Press Windows+R keys to open the Run window, type “secpol.msc” and press Enter.
- On the right pane, locate the policy Interactive Logon: Number of previous logins attempts to cache (if the domain controller is unavailable).
- Double-click it to edit its settings.
- Change the value if “Do not cache logins” to 0.
Change the DNS server address
- Press Windows+R to open the Run window. Type the command ncpa.cpl.
- Press Enter to open the Network connections window.
- Right-click on your network adapter and select Properties.
- You might need administrator permission for the same.
- Double-click on Internet Protocol Version 4 to open its properties.
- Shift the radio button to Use the following DNS server address.
- Enter the following values:
- Preferred DNS address: 8.8.8.8
- Alternate DNS address: 8.8.4.4
- Click on OK to save the settings and reboot the system.
Disable antivirus
Sometimes security software, such as antivirus and even Windows defender anti-virus, may cause issues with your account. This happens due to the fact that some programs don’t allow multiple instances of themselves running at once. So, if you’re having trouble logging in using your credential or getting notifications, there are a few things we recommend doing to fix the problem.
If you use Windows 10, here’s how to disable the real-time security feature, which is enabled by default. If you want to turn off the antivirus altogether, follow the next set of instructions.
- Open Start.
- Search for Windows Security and click on the top result to launch the program.
- Click on Virus & Threat protection.
- Scroll down to Real Time Protection Settings.
- Select Turn Off.
- Restart your computer.
Disabling Windows Defender Antivirus
To disable Windows Defender Antiviruses permanently, follow these steps:
- Open Start.
- Search for gpedit. ms c and click the top result.
- Double-click the Turn Off Windows Defender Antivirus Policy item.
- Select the Enabled option to turn off Windows Defender Antiviral software.
- Click the Apply button. You’ll see a confirmation screen. If you don’t want to disable Windows Defender Antimalware, simply select the Disabled option.
- Close the Local Group Policy Editor window.
Expert Tip: This repair tool scans the repositories and replaces corrupt or missing files if none of these methods have worked. It works well in most cases where the problem is due to system corruption. This tool will also optimize your system to maximize performance. It can be downloaded by Clicking Here
Frequently Asked Questions
How to fix the 'we can't sign you in with this credential' issue
- Reboot the system with no network connectivity.
- Using Security Policy snap-in.
- Change the DNS server address.
- Remove the user from the protected user group.
What is the reason for 'we can't sign you in with this credential' error
A PC or laptop belonging to an organization must be verified before it can be used. It makes sure that the system doesn't waste its resources before they're authorized. If the PC cannot connect to the domain via the local network or the internet, then the computer will display this error message.
How do I stop Windows from asking for credentials?
Windows asks for credentials when you try to access a resource that requires authentication. For example, when you try to access your email account, Windows prompts you for your username and password. The reason why Windows needs to authenticate you is that it wants to make sure that you have permission to access the resource.